Hack it security through penetration testing
Hack I.T.: Security Through Penetration Testing. T. J. Klevinsky. Scott Laliberte. Ajay Gupta. Publisher: Addison Wesley. First Edition February 01,
Hack I.T. - Security Through Penetration Testing


Hi, i am Lilian Age: 27. Make sure you take time out of your busy schedule to rejuvenate and pamper yourself with me Kimmy ??Having worked in a corporate environment on management position for several years made me very tired and I realized it is not the job I wish to continue at - nowadays escorting gives me freedom and joy to meet gentlemen from different backgrounds and various parts of the world on one hand and to focus on my time the way I wish to on the other hand







Hack I.T. - Security Through Penetration Testing [T. J. Klevinsky, Scott Laliberte, Ajay Gupta] on www.ecsac.eu *FREE* shipping on qualifying offers.


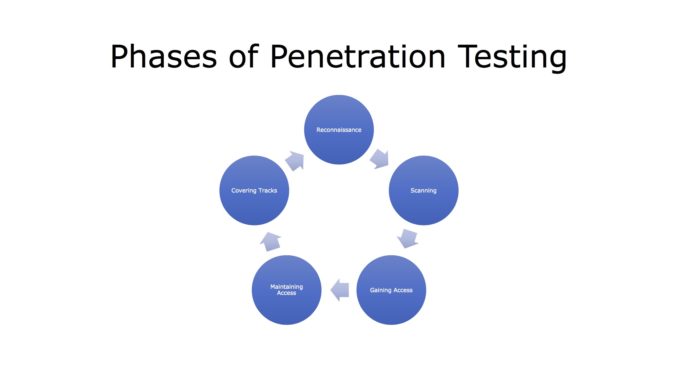
Description:Gsecurity provides cyber security and data privacy services to federal, state, and local governments, as well as commercial clients in the educational, financial, and health-care sectors. He has been quoted as a security expert in the Financial Times, Securities Industries News, and elsewhere, and has authored numerous information security articles for a variety of publications. Hacking myths Potential drawbacks of penetration testing Announced versus unannounced testing Penetration through the Internet, including zone transfer, sniffing, and port scanning War dialing Enumerating NT systems to expose security holes Social engineering methods Unix-specific vulnerabilities, such as RPC and buffer overflow attacks The Windows NT Resource kit Port scanners and discovery tools Sniffers and password crackers. Most importantly, the book provides a framework for performing penetration testing and offers step-by-step descriptions of each stage in the process. Specific topics covered in this book include:





























User Comments 2
Post a comment
Comment: